TSCM & Bug Sweeping
Protecting the confidentiality of your conversations, meetings and decisions.
Technical Surveillance Counter-Measures for corporate, residential and maritime environments. Structured detection, documented assurance, complete discretion.
The room looks clean. The meeting happened in a space you use every week. Nobody new was in the building. The conversation that followed still turned up somewhere it should not have. Technical Surveillance Counter-Measures exists for exactly this: the moment when clean-looking is no longer enough.
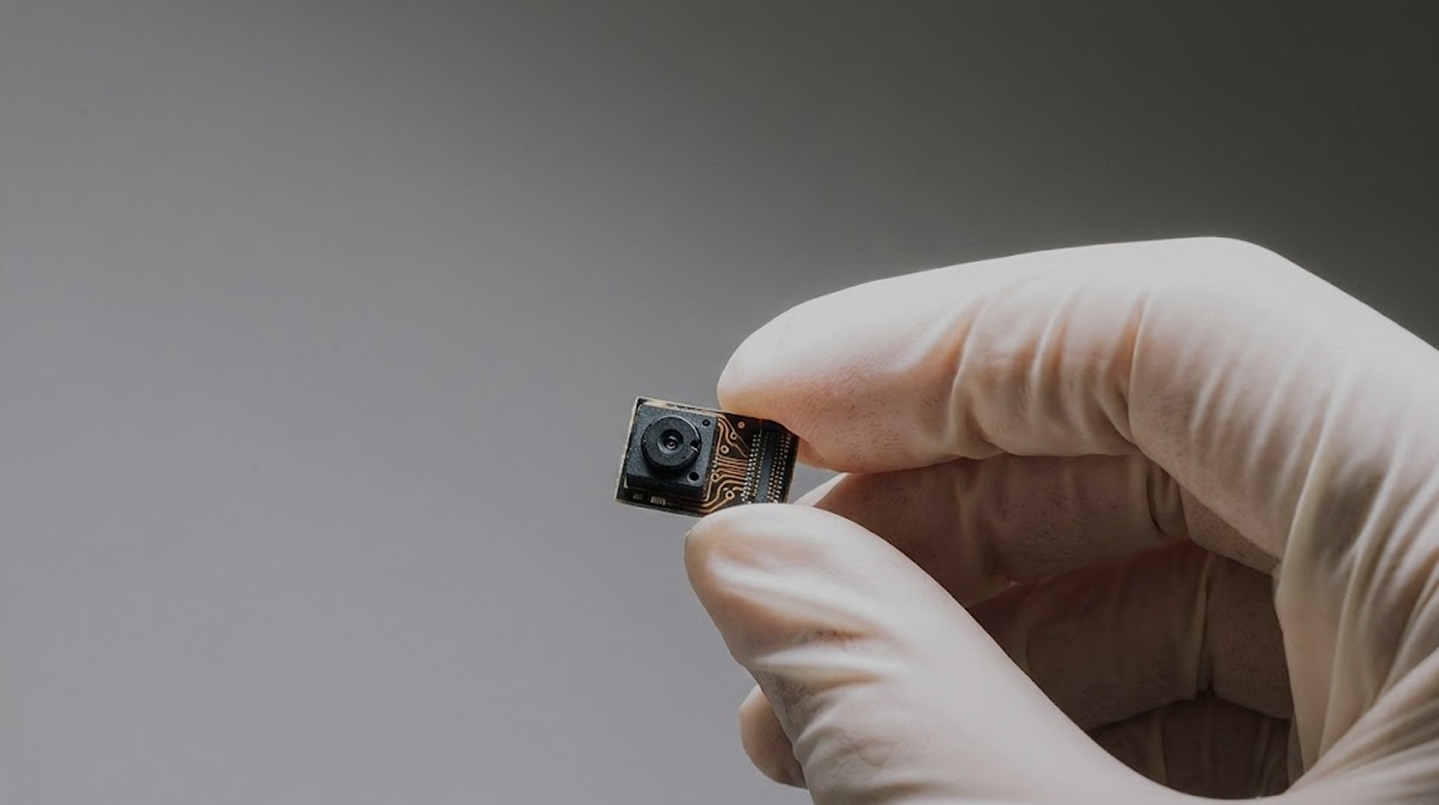
Technical Surveillance Counter-Measures (TSCM), sometimes called bug sweeping, is the structured process of detecting, identifying and addressing electronic eavesdropping threats. For organisations and individuals handling genuinely sensitive information, TSCM is an ongoing discipline that protects the integrity of your most important environments.
Technical Surveillance Counter-Measures (TSCM), sometimes called bug sweeping, is the structured process of detecting, identifying and addressing electronic eavesdropping threats. For organisations and individuals handling genuinely sensitive information, TSCM is an ongoing discipline that protects the integrity of your most important environments.
clients
Who we work with


Corporate and Transactions
Strategic discussions, M&A activity, data rooms and sensitive board processes. Surveys timed to transaction milestones, board cycles and critical decision points, from initial approach through to completion.

Law Firms and Legal Counsel
Matters where privileged communications must remain privileged. Survey reports documented to support legal proceedings and professional obligations.

Family Offices and UHNW Principals
Residences, vehicles, yachts and travel. Discreet, scheduled surveys for clients whose personal and professional lives demand the same standard of protection.

Maritime Clients
Environments where access control is complex and surveillance risk is elevated. Vessel surveys covering cabins, meeting spaces, communications infrastructure and shoreside facilities.

Event Organisers
High-profile convenings, investor summits and executive retreats. Pre-event surveys of venues, breakout spaces and technical infrastructure.

Security Assessment
What you receive
A Grey Prism TSCM engagement tells you exactly what the threat picture is in your environment.
How it works
How an engagement works
.jpg)
01
Initial consultation
A confidential conversation to understand your concerns, your environment and what you need to know by the end of it. This shapes the scope and approach.
02
Risk assessment
An assessment of the threat profile before any survey begins: who might target you, what methods they might use, and which environments are most exposed. The survey is more useful when it knows what it is looking for.
03
Physical inspection and radio frequency analysis
A systematic survey of the agreed spaces. Radio frequency detection across the usable spectrum, non-linear junction detection for dormant or passive devices, thermal analysis, power line analysis and detailed physical inspection. Offices, boardrooms, vehicles, vessels, temporary meeting rooms and private residences.
04
Secure reporting
A written report delivered through agreed secure channels. Findings, assessed risk and specific recommendations for decision-making at leadership level.
05
Mitigation and follow-up
Where vulnerabilities are identified, you receive immediate mitigation guidance and longer-term controls. Where devices are found, you receive advice on evidence handling, legal options and next steps. Periodic survey programmes can be designed to maintain assurance over time.
why grey prism
Grey Prism combines strategic advisory, intelligence capability, and discreet operational support to help organisations manage risk with clarity and confidence.
FAQs
Common questions
What is Technical Surveillance Counter-Measures?
Technical Surveillance Counter-Measures is the formal term for the detection and resolution of covert surveillance threats. It is sometimes called bug sweeping or electronic counter-surveillance. Professional TSCM uses advanced instrumentation and structured methodology to identify threats that consumer-grade detection equipment would miss.
How long does a survey take?
It depends on the environment and the number of technicians. A single boardroom might take several hours. A full corporate floor or large residence will typically require a full day or more. Every engagement is scoped in advance based on space, threat profile and the level of assurance required.
What environments do you survey?
Offices, boardrooms, conference facilities, sports facilities, private residences, vehicles, yachts, aircraft, hotel rooms and temporary meeting spaces.
What if nothing is found?
A clean survey is a valuable outcome. You receive a documented record that the environment was clear at the time of the sweep, which supports governance, legal proceedings and ongoing risk management. Many clients run periodic surveys specifically to maintain that record.
Can we engage you on a retainer?
Yes. Retainer arrangements and scheduled survey programmes are available, tied to governance calendars, transaction timelines or risk profiles. They are designed to provide ongoing assurance rather than a single snapshot.
How do you handle confidentiality and discretion?
Every engagement is governed by NDAs, controlled communications and scheduling designed to minimise visibility. Work is planned around your operations. Presence on site is managed so that, for most clients, the process is entirely unobtrusive.
.webp)


.jpg)


.jpg)






.webp)