Aerial Intelligence & Counter-UAS Advisory
Security-focused aerial assessments and counter-UAS readiness for corporate, commercial, and private clients.

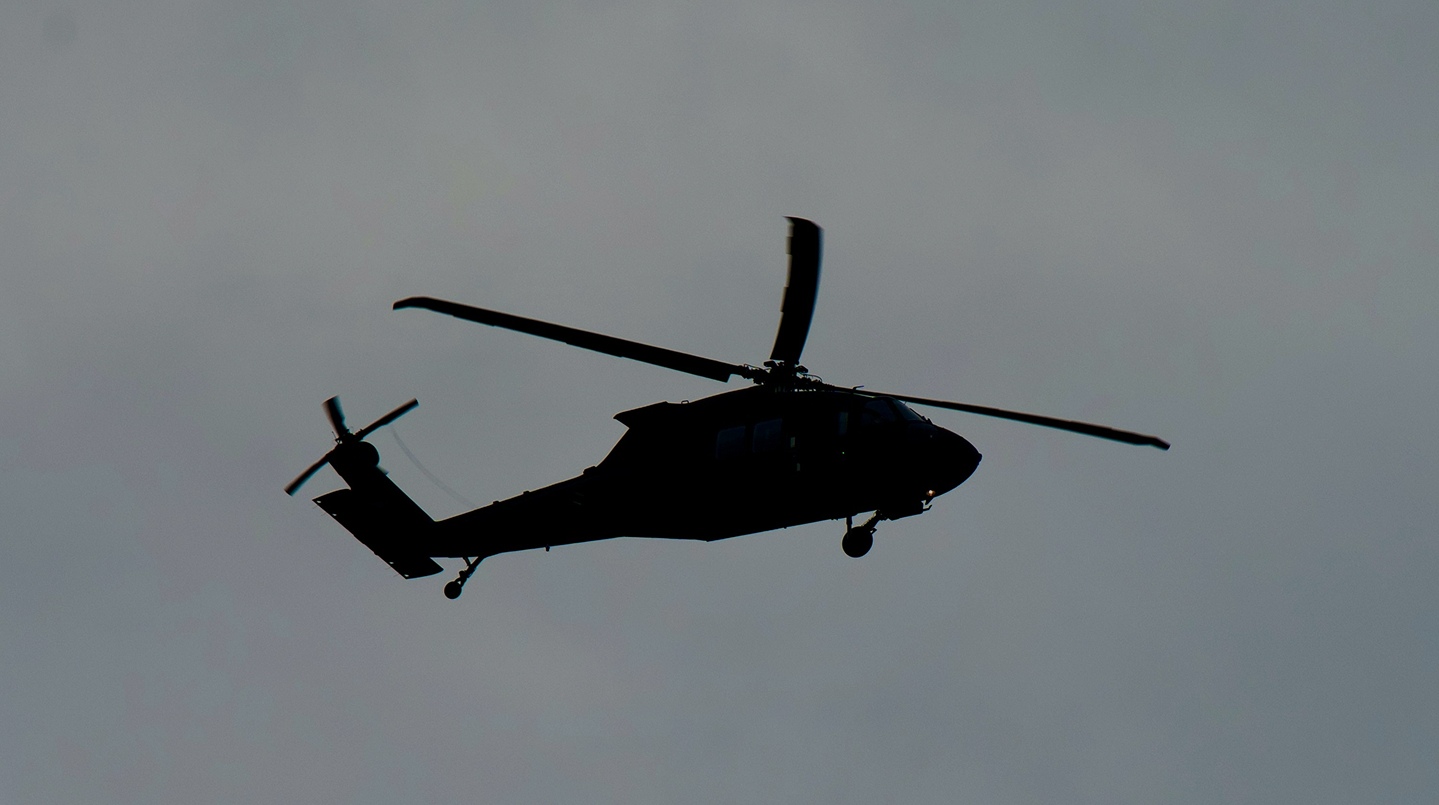
When a drone flies over a site, it sees what ground-level security cannot. The approach line that avoids every sensor on the perimeter. The skylight that nobody ever thinks about. The gap between the fence line and the camera's field of view.
Grey Prism works with this in two directions. The first is using aerial operations to show clients exactly what their site reveals from above — the view an adversary could already have. The second is preparing organisations for when the drone is the threat: the surveillance operation, the perimeter breach, the event they have no procedure for. Both capabilities sit inside the same engagement. The assessment informs the readiness plan.
clients
Who this is for


Corporate Security & Facilities
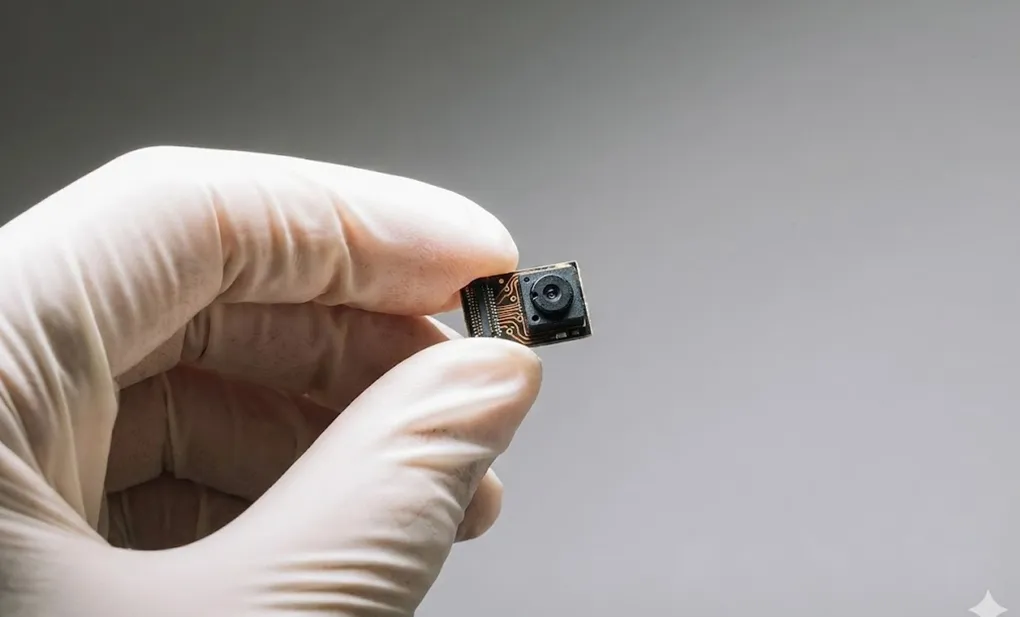
A drone at altitude can read documents on a screen through a sixth-floor window and stay outside the field of view of most corporate CCTV. Most corporate security was built for threats that arrive at ground level.

Private Estates & Family Offices
A drone can see into a private estate — its grounds, its access points, its windows — in ways that no fence or ground-level camera was designed for. Grey Prism is commissioned by estate principals and family offices to understand exactly what their property reveals from above.

Events & Venues
Venues and event organisers face aerial threats they cannot physically stop. From 2027, Martyn's Law will require venues in scope to show that they have considered a range of threats, including drones, as part of their security planning. If a drone appeared over your event tonight, would your team know what to do?

Maritime & Port Security
Port and maritime environments have aerial exposure that ground-level security was not built to address. Grey Prism and Sentinel Flight Services are consulted by port operators, vessel operators, and maritime security teams — in the UK and internationally — to assess what their environment reveals from above, and where the gaps in their security picture are.

Insurance & Risk Management
Insurers and risk committees are asking for documented evidence that aerial threats have been assessed. An aerial assessment gives them what they need. Something solid to point to.
insight
Martyn's Law readiness
The Terrorism (Protection of Premises) Act 2025, commonly known as Martyn's Law, received Royal Assent in April 2025. It is not yet in force, with an implementation period of at least 24 months, and is expected to commence during 2027. The Act introduces new obligations for premises and events where 200 or more people may be present.
Grey Prism supports organisations in understanding whether they fall within scope, assessing current preparedness, and developing the procedures, documentation, and staff readiness the Act will require.
Grey Prism supports organisations in understanding whether they fall within scope, assessing current preparedness, and developing the procedures, documentation, and staff readiness the Act will require.

Insight
Understanding Martyn's Law — what it means for your premises
read more

Security Assessment
Aerial Security Assessments
Everything below comes from a single question: what would someone with a drone already know about this place?
How it works
How an engagement works

01
Initial consultation.
A private discussion to understand your site, your concerns, and what you need. Most engagements cover both aerial assessment and counter-UAS readiness once the aerial view of the site is established.
02
Threat and risk assessment.
Before any physical audit begins, we assess the threat landscape relevant to your premises, your sector, and your profile.
03
On-site security audit.
A structured assessment of your physical environment, security infrastructure, procedures, and personnel.
04
Analysis and reporting.
A written report containing findings, assessed risk levels, and prioritised recommendations.
05
Implementation and follow-up.
Where required, we oversee the implementation of recommended enhancements and provide ongoing advisory support.
why grey prism
Grey Prism combines strategic advisory, intelligence capability, and discreet operational support to help organisations manage risk with clarity and confidence.
FAQs
Frequently asked
questions
What is the difference between a security audit and a risk assessment?
A security audit evaluates what is currently in place. A risk assessment looks at the threats you face and how vulnerable you are to them. We typically do both, because recommendations need to be grounded in the threat picture as well as the current state of your security.
How long does an assessment take?
It depends on the size and complexity of the environment. A single corporate office might take one to two days on-site. A multi-site portfolio, a large estate, or a maritime assessment will take longer. We scope every engagement before it begins.
How disruptive is the process?
A security audit evaluates what is currently in place. A risk assessment looks at the threats you face and how vulnerable you are to them. We typically do both, because recommendations need to be grounded in the threat picture as well as the current state of your security.
What does it cost?
A security audit evaluates what is currently in place. A risk assessment looks at the threats you face and how vulnerable you are to them. We typically do both, because recommendations need to be grounded in the threat picture as well as the current state of your security.
Is the process confidential?
A security audit evaluates what is currently in place. A risk assessment looks at the threats you face and how vulnerable you are to them. We typically do both, because recommendations need to be grounded in the threat picture as well as the current state of your security.
What environments do you assess?
A security audit evaluates what is currently in place. A risk assessment looks at the threats you face and how vulnerable you are to them. We typically do both, because recommendations need to be grounded in the threat picture as well as the current state of your security.
Can you help implement your recommendations?
A security audit evaluates what is currently in place. A risk assessment looks at the threats you face and how vulnerable you are to them. We typically do both, because recommendations need to be grounded in the threat picture as well as the current state of your security.
.webp)











.webp)